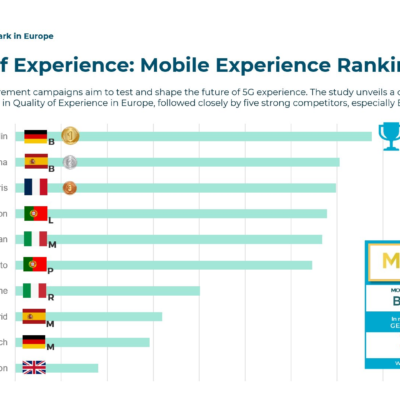
The capability of 5G is unquestionable, as it has the potential to reshape economies and that is why most of the countries are also worried about the inevitable security issues that come with the deployment of 5G technology.
The biggest worry of the government is “If the deployed 5G Technology is safe enough to use as a communication medium by its citizen and the government?”
To mitigate this concern, Belgium has been working on a High-Risk Vendor list that won’t be published openly. The entity behind defining this list is The Veiligheid van de Staat – Sureté de l’État (VSSE) and Algemene Dienst Inlichting en Veiligheid (ADIV), which are the secret agencies of Belgium. The whole process of identifying the security risk related to 5G rollout is kept as a Black box.
What criteria Belgium has set, to define the High-Risk Vendor list? As the whole process of defining the list is confusing and a mystery”
The industry and consumers are concerned about the decisions made behind closed doors that are taken in Brussels. There is only one way to address the issues of national security concerns, make the whole process of defining the high-risk vendor list open to the public for debate. It is high time the national governments realize that transparency is the key to move forward in the right direction as nothing good comes out of closed doors decisions. People have a right to know what their governments are planning and doing with the future of their country.
No one in Belgium would like Blackbox operation
One of my friend said
It seems that Brussels is being pressurized by a foreign entity to block certain 5G suppliers
If the process of defining the High-Risk Vendor list is not made transparent, it could result in gravely impacting the swiftness of 5G rollout and the cost of 5G equipment could go remarkably high. Who is going to suffer from this situation the most? Of course, the consumer…
Another possibility of secretly defining the High-Risk Vendor list is to allow only a handful of 5G Suppliers to participate in 5G rollout and therefore to create a monopoly in otherwise a free market. This in turn would destabilize the market and will end up demotivating new entrants to do business in a biased market.
Brussels must realize that we are in a critical time of 5G infrastructure deployment. The government should act now to ensure that they implement a technology-neutral environment in which all the suppliers can fairly compete against each other. This will ensure that everyone will have the access to 5G services in a shorter period of time.